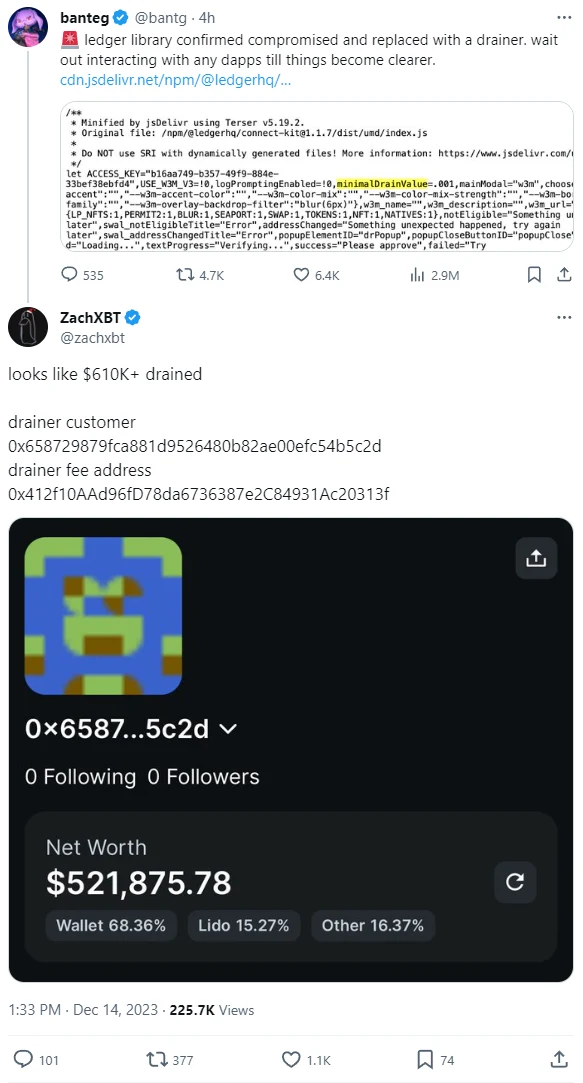
https://twitter.com/zachxbt/status/1735292040986886648
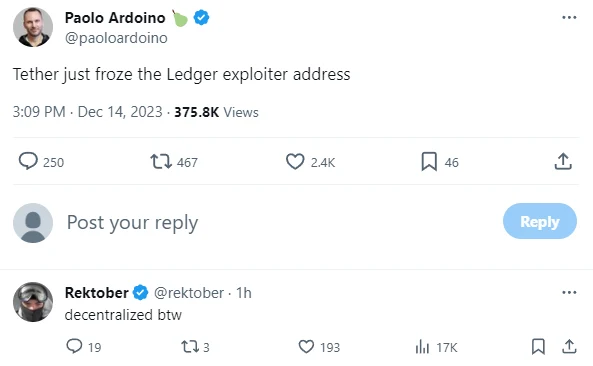
https://twitter.com/paoloardoino/status/1735315976827101274
Abridged summary from Ledger themselves:
This morning CET, a former Ledger Employee fell victim to a phishing attack that gained access to their NPMJS account.
The attacker published a malicious version of the Ledger Connect Kit (affecting versions 1.1.5, 1.1.6, and 1.1.7). The malicious code used a rogue WalletConnect project to reroute funds to a hacker wallet.
Ledger's technology and security teams were alerted and a fix was deployed within 40 minutes of Ledger becoming aware. The malicious file was live for around 5 hours, however we believe the window where funds were drained was limited to a period of less than two hours.
The genuine and verified Ledger Connect Kit version 1.1.8 is now propagating and is safe to use.
For builders who are developing and interacting with the Ledger Connect Kit code: connect-kit development team on the NPM project are now read-only and can't directly push the NPM package for safety reasons.
We have internally rotated the secrets to publish on Ledger's GitHub.
Ledger, along with Walletconnect and our partners, have reported the bad actor's wallet address. The address is now visible on chainalysis
Tether_to has frozen the bad actor's USDT.
We are actively talking with customers whose funds might have been affected, and working proactively to help those individuals at this time.
We are filing a complaint and working with law enforcement on the investigation to find the attacker.
We're studying the exploit in order to avoid further attacks. We believe the attacker's address where the funds were drained is here: 0x658729879fca881d9526480b82ae00efc54b5c2d








Jump in the discussion.
No email address required.
i got a trezor this week, so feeling good about that judgement call
Jump in the discussion.
No email address required.
More options
Context