- 36
- 16
Here is the cipher. The question  has been scrambled from its original form.
has been scrambled from its original form.
Here is the key:
The first  to give me the answer
to give me the answer  to the question
to the question  will get 10k MB and a unique badge. The only hint I will give is that I started with the Caesar
will get 10k MB and a unique badge. The only hint I will give is that I started with the Caesar  cypher method. Badge
cypher method. Badge  should
should  be ready
be ready  in the next few days or so. The next 4 will get 10k mb.
in the next few days or so. The next 4 will get 10k mb.
!ghosts would  someone in badgemaxxers mind pinging them please?
someone in badgemaxxers mind pinging them please?
- 21
- 25
hi guys, i am looking for sites to add to my webring! gimme ur urls :p thanks @X for suggsting neocities!
- 33
- 53
- 73
- 68
How Freedesktop/RedHat harass other projects into submission
https://blog.vaxry.net/articles/2024-fdo-and-redhat
Freedesktop/RedHat's CoC team is worse than you thought
https://blog.vaxry.net/articles/2024-fdo-and-redhat2
Strags respond
https://drewdevault.com/2024/04/09/2024-04-09-FDO-conduct-enforcement.html
- 23
- 35
The Official RDrama Computer Science Reading Group
My dear !codecels, hello and welcome to the first meeting of RDrama's Computer Science Reading Group! Here's the idea - we (read: I) pick a computer science textbook, then post a list of sections and exercises from that textbook each week. In the thread, feel free ask questions, post solutions, and bully people for asking stupid questions or posting stupid solutions. If you don't want to read along, I'll post the complete exercises in the OP, so you can solve them without needing to read the book.
SICP
The book I'm starting with is 'the Structure and Interpretation of Computer Programs' (abbreviated SICP). It's a software engineering textbook written by Gerald Jay Sussman and Hal Abelson from MIT. The book builds programming from the ground up: starting with a very simple dialect of Scheme and growing it into a language with lazy evaluation, object-orientation and a self-hosting compiler. It's a fun book: the exercises are hands-on and interesting, the writing is informative without being droll, and both the book itself and a corresponding lecture series (complete with a 80s synth rendition of 'Also Sprach Zarathustra') are available for free online.
Languages
The book uses (a small subset of) Scheme as its primary language, but feel free to try using a different language. The book's dialect of scheme is available through Racket, but most lisps will work with only minor changes. Other dynamically-typed, garbage-collected languages with higher-order functions will also not require much hacking: there is an edition written in JavaScript  , as well as a partial adaptation to python
, as well as a partial adaptation to python  . High-level, statically typed languages might also work: Java/Kotlin/C#
. High-level, statically typed languages might also work: Java/Kotlin/C#  seem doable, but I don't know those languages well. Strongly typed languages like Haskell will require some real hacks, and I'd avoid doing it in C, C++ or Rust.
seem doable, but I don't know those languages well. Strongly typed languages like Haskell will require some real hacks, and I'd avoid doing it in C, C++ or Rust.
Exercises
The book is split into five chapters:
- Building Abstractions with Procedures
- Building Abstractions with Data
- Modularity, Objects and State
- Metalinguistic Abstraction
- Computing with Register Machines
This week, I'll be posting exercises from the first chapter. The chapter is pretty easy for those familiar with programming already, so I just want to get it out of the way. Here are the selected exercises:
Exercise 1.8
Newton's method for cube roots is based on the fact that if
yis an approximation to the cube root ofx, then a better approximation is given by the value(x/y² + 2y) / 3. Use this formula to implement a cube-root procedure which is wrong by at most0.01.
Exercise 1.12
The following pattern of numbers is called Pascal's Triangle.
1
1 1
1 2 1
1 3 3 1
1 4 6 4 1
...
The numbers at the edge of the triangle are all 1, and each number inside the triangle is the sum of the two numbers above it. Write a procedure that computes elements of Pascal's triangle.
Exercise 1.18
Devise a procedure generates an iterative process for multiplying two integers in terms of adding, doubling, and halving and uses a logarithmic number of steps.
Exercise 1.31
Write a procedure called
productthat returns the product of the values of a function at points over a given range (product(l, r,step,f) = f(l) * f(l+step) * f(l + 2 * step) * ... * f(r)). Show how to definefactorialin terms ofproduct. Also use product to compute approximations to using the formulaπ/4 = (2 * 4 * 4 * 6 * 6 * 8 ...) / (3 * 3 * 5 * 5 * 7 * 7 ...)
Exercise 1.43
If
fis a numerical function andnis a positive integer, then we can form thenth repeated application off, which is defined to be the function whose value atxisf(f(...(f(x))...)). For example, iffis the functionx → x + 1, then thenth repeated application offis the functionx → x + n. Iffis the operation of squaring a number, then thenth repeated application offis the function that raises its argument to the2 * nth power. Write a procedure that takes as inputs a procedure that computesfand a positive integernand returns the procedure that computes thenth repeated application of f. Your procedure should be able to be used as follows:repeated(square,2)(5) = 625
Have fun! 
- 12
- 44
Potential sites to farm drama 
- 4
- 17
They want you to print that shit on a piece of paper or login to your Microsoft account in case you forget it 
- 38
- 57
Lots of great comment threads under it too, pure 
- 5
- 11
- 40
- 80
- 20
- 17
hi, im learning some html in class right now, but it's all just .html files on my computer, how do i add it to the web? preferably for free, also i dont want it to be slow
- 38
- 120
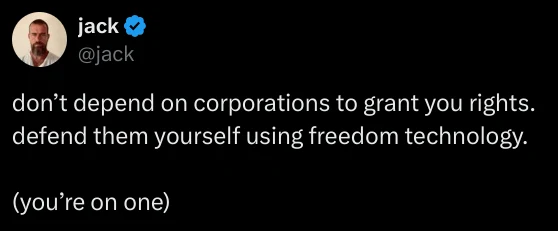
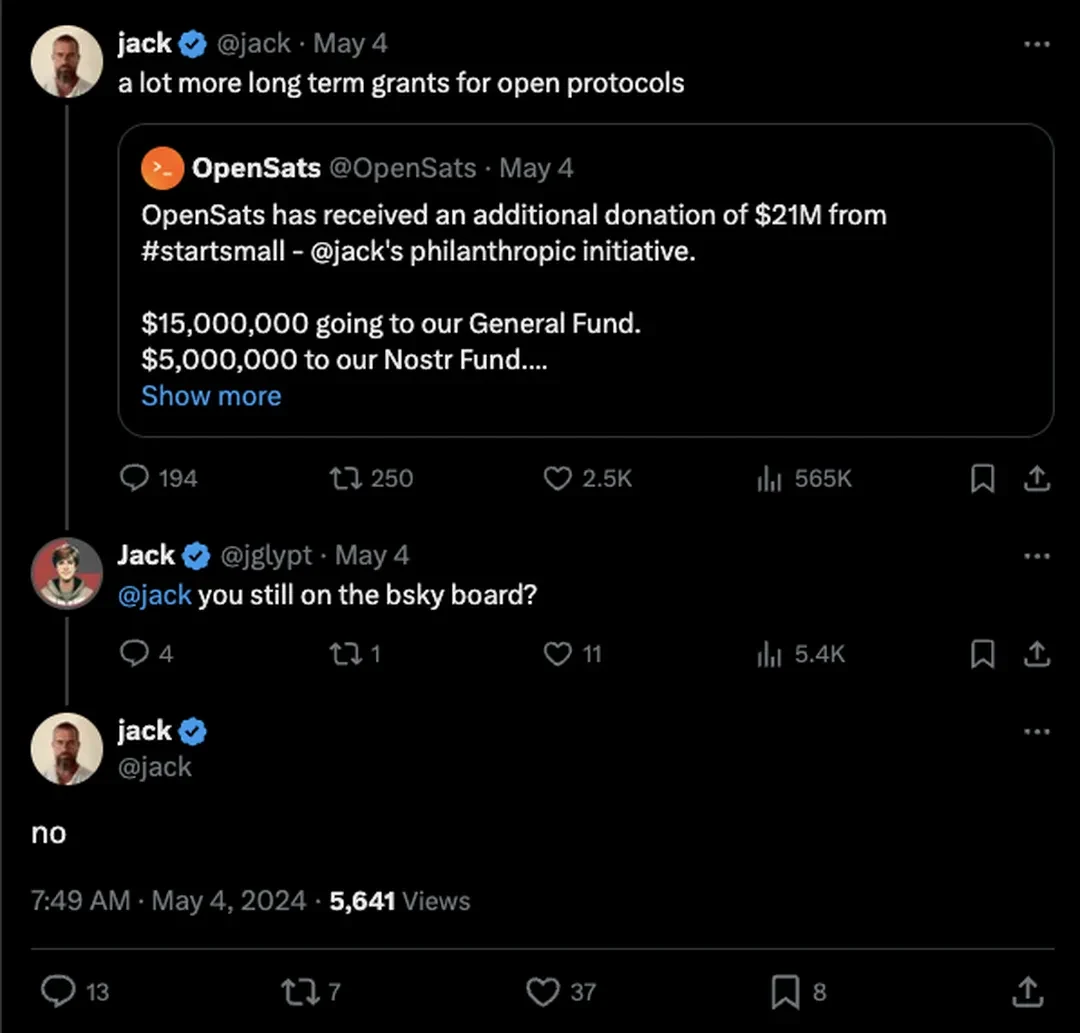
Twitter founder Jack Dorsey is no longer on the board of Bluesky, the decentralized social media platform he helped start. In two posts today, Bluesky thanked Dorsey while confirming his departure and adding that it's searching for a new board member “who shares our commitment to building a social network that puts people in control of their experience.”
The posts come a day after an X user asked Dorsey if he was still on the company's board, and Dorsey responded, without further elaboration, “no.” As TechCrunch points out, Dorsey was on a tear yesterday, unfollowing all but three accounts on X while referring to Elon Musk's platform as “freedom technology.”
Neither Bluesky nor Dorsey himself seem to have said how or why he left the board. For now, two board members remain: CEO, Jay Graeber, and Jabber / XMPP inventor Jeremie Miller. Dorsey originally backed Bluesky in 2019 as a project to develop an open-source social media standard that he wanted Twitter to move to. He later joined its board of directors when it split from Twitter in 2022.
But Dorsey hadn't seemingly been a particularly active participant at the company. In March, when The Verge's Nilay Patel asked Graeber for Decoder about his level of involvement with Bluesky, she said she gets “some feedback occasionally,” but implied he's otherwise “being Jack Dorsey on a cloud,” as Nilay put it. Months before that interview, Dorsey had closed his Bluesky account.
Bluesky did not immediately respond to The Verge's request for comment.
Update May 5th, 2024, 4:37PM ET: Updated with Bluesky's confirmation of Dorsey's departure from its board.
- 57
- 102
TunnelVision, as the researchers have named their attack, largely negates the entire purpose and selling point of VPNs, which is to encapsulate incoming and outgoing Internet traffic in an encrypted tunnel and to cloak the user's IP address. The researchers believe it affects all VPN applications when they're connected to a hostile network and that there are no ways to prevent such attacks except when the user's VPN runs on Linux or Android. They also said their attack technique may have been possible since 2002 and may already have been discovered and used in the wild since then.
( . . . . )
Interestingly, Android is the only operating system that fully immunizes VPN apps from the attack because it doesn't implement option 121. For all other OSes, there are no complete fixes. When apps run on Linux there's a setting that minimizes the effects, but even then TunnelVision can be used to exploit a side channel that can be used to de-anonymize destination traffic and perform targeted denial-of-service attacks. Network firewalls can also be configured to deny inbound and outbound traffic to and from the physical interface. This remedy is problematic for two reasons: (1) a VPN user connecting to an untrusted network has no ability to control the firewall and (2) it opens the same side channel present with the Linux mitigation.



- 5
- 13
- 44
- 148
- 89
- 69
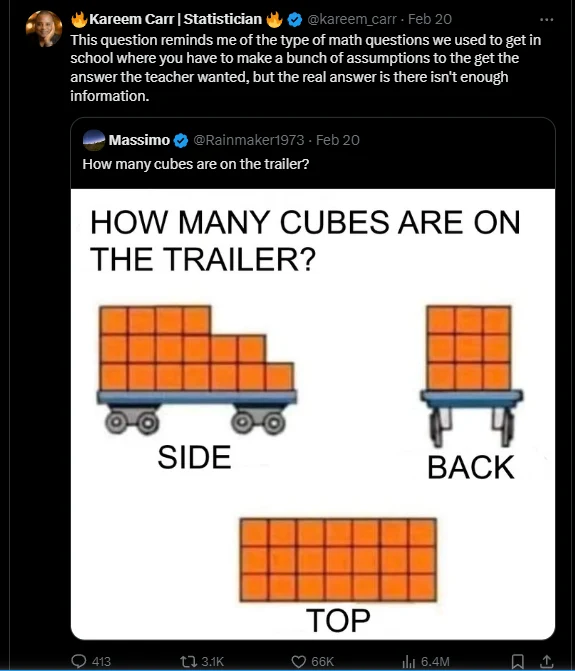
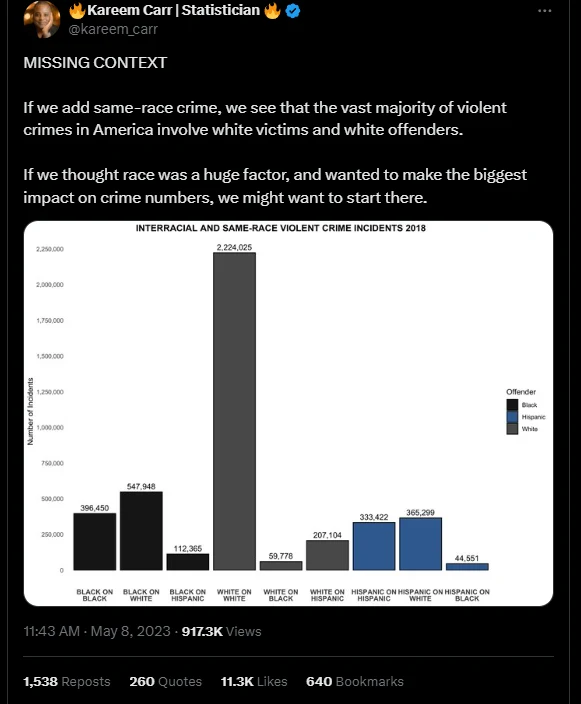
For the uninitiatied: This is the absolute r-slur who spent weeks arguing that "2 + 2 ≠ 4"
https://www.westernjournal.com/wokeness-comes-mathematics-academics-saying-225/
He's also famous for making sophomoric ggplot charts in R to show off his "data science" chops 
and going viral for bullshit like this:

 Unique Badge!
Unique Badge! 
 to solve this Cipher! First
to solve this Cipher! First 








 from contributing to freedesktop : linux
from contributing to freedesktop : linux  | Man fails to respect
| Man fails to respect  the CoC and gets banne by loser
the CoC and gets banne by loser  wokescold with an email job
wokescold with an email job













 I'm like a dog chasing waterfalls
I'm like a dog chasing waterfalls











 about how
about how 





 Diversity Is Our Strength
Diversity Is Our Strength 

















 IMPORTANT
IMPORTANT 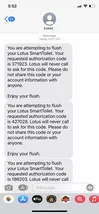





 "Data Scientist" (Kareem Carr) thinks that "Python is a massive pain in the butt to install"
"Data Scientist" (Kareem Carr) thinks that "Python is a massive pain in the butt to install"